Blog / Leadership & Transformation
Is Blockchain Hackable?
Categories

In this article, the lecturer of Computer Science in our Global Master's in Blockchain Technologies and an IT professional, Cedric Mössner, sets out to answer the question: is blockchain hackable?
Blockchain technologies are one of the new breaking technologies of the decade. They are said to have the power to revolutionize our financial system. However, as the financial system is a very attractive target for hackers, it is not uncommon to come upon news about hacked blockchain exchanges. But saying that the blockchain technology itself was hacked, isn’t technically correct. It wouldn't be that easy or even possible for the blockchain to be hacked.
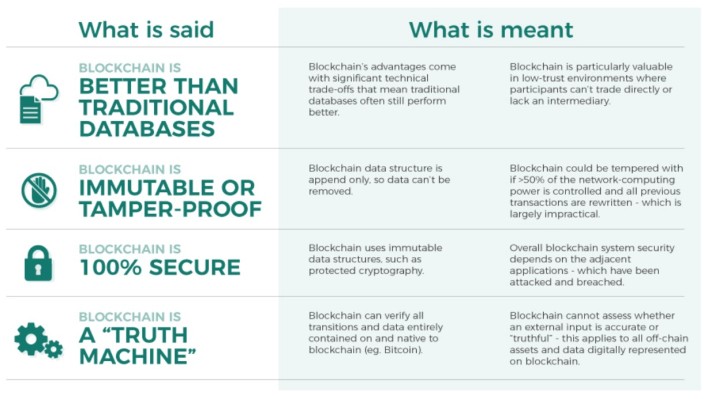
For starters, in order to have a clearer overview of what blockchain really is, we can take a look at the image below to grasp what does it actually mean when we say that blockchain is tamper-proof or a truth machine. In the left column, you can observe the affirmations often made about blockchain. In the right column, you can find out what is actually meant by them.
What are the security guarantees of a blockchain?
First, in our quest to prove that blockchain is hard to hack, we shall observe its unique features that have contributed to it being called a "tamper-proof technology".
Privacy of the users
Blockchain technologies rely on cryptography, which is why the coins built on it are also called cryptocurrencies. The groundbreaking novelty is that the financial records are not privately owned by a bank, but they are publicly available. Everyone can participate in the network and download the records. In this design, however, it doesn't result in vulnerability, as no real names, but pseudonymous addresses are used. This, in turn, permits to protect the users, as even the bank employees can’t access your balance. There are even more cryptographic mechanisms involved to protect the privacy of users. In the case of some currencies, it isn’t possible to know who sends money to whom by viewing the very logs of the transaction.
Integrity of the data
The next protection objective in any application is the integrity of the data. Data may only be altered by the ones who should have access. There shouldn't be anyone else altering it neither on the way of transportation nor in the database. And that's where blockchain outshines other solutions.
The concept allows the blockchain database to be deployed to every user. If any of the data is altered, the network recognizes the changes and just rejects them. This is done by hash functions that are used within the blockchain. Hashes are well proven cryptographic building blocks, examined by the best cryptographs for years. The most powerful supercomputers have been used to try to break the hash functions of the most popular coins, and it is calculated that finding one single collision will take more than 10000 years.
Hash functions produce, simply said, an unpredictable output which is consistently the same, if the input remains the same. This function is used to connect the blocks of the blockchain into a chain. If an earlier block is altered, every following block changes entirely. Therefore, other clients can detect changes instantly.
Availability
The last goal of protection is availability. This is easily achieved, as every participant of the network will further strengthen the network. For the network to fail, an attacker would have to take down every single user, which is near to impossible.
What are the security risks of blockchain?
However resistant to attacks, even blockchain technologies cannot be considered completely immune. In what follows, we will dissect the possible shortcomings of blockchain or rather that of its users, and how common that sort of security breach really is.
“Double spend attack”
There is one attack scenario, which is unique to blockchain. Creating new blocks containing the transactions from the users is done not by a centralized government but by the users themselves. Therefore, it is possible to spend the same “coin” more than once.
To cope with this issue, every blockchain technology has a consensus method like Proof of Work or Proof of Stake. These work like a form of authorization for block creation and distribute the rights fairly among users. It is still possible to perform this kind of attack, although very expensive.
For example, the bitcoin network uses Proof of Work to prevent this “double spend attack”. To carry it out, an attacker needs more than 50% of the hashing power of the network. This would be equivalent to more than twice the amount of all graphics cards available in the entire world market right now and is therefore practically impossible (and way too expensive also).
Implementation issues
Implementation and usage issues are among the problems not completely solved yet. Many of the smaller coins could have issues in their code basis, that could lead to exploitation.
Furthermore, as the world of cryptocurrencies is advancing way faster than the world of cryptography, most of the coins are submitted as white papers, which are not peer-reviewed and may contain severe logical issues. That, however, needs to be determined for every coin itself and might as well be true for online banking portals.
In fact, cryptocurrencies are usually open-source. That means, everybody can and many users will read parts of the code and the white paper. This leads to some kind of open intelligence. Users who find bugs still want their money to be safe and therefore help to fix the issues by reporting it. Online banking portals are not open-source and are thus not inspected by users. Bugs in these closed-source environments are consequently only searched by employees. Hence, most of the time, a cryptocurrency will be more secure than an online banking portal.
Usage issues
Usage issues are a different topic, however. This is where most of the hacks happen. Since cryptocurrencies are not that easily traced, stealing funds is almost as untraceable as purse snatching. This is why many hackers focus on individuals or companies working with cryptocurrencies to make a mistake of which they could take advantage. However, this is not a shortcoming of the cryptocurrency but rather of the ones using it.
Quantum computers
Lastly, there is always the fear of cryptography in the face of quantum computers. Many people think, that all cryptography will be broken as soon as quantum computers have as many qubits as the cryptographic algorithm. This is not true.
Until now, it is only proven, that the RSA assumption will not hold with quantum computers, because there is an efficient algorithm to factorize large numbers. Many of the asymmetric algorithms can, in fact, be reduced – that means reformulated – as the RSA problem and are through that broken. That is not the case for hash functions. Until now, there is no algorithm on quantum computers that can revert them.
That, however, does not mean anything. As far as we know right now, it could still be true (although unlikely) that P = NP, which would break the entire field of computer science. But up until now, blockchain technologies are not broken even in the face of quantum computing although there is a lot of research going on in that field.
For online banking, this cannot be said. Online banking relies on asymmetric cryptography and will be broken for sure when quantum computers are available. There are of course alternatives, but still, cryptocurrencies are the better option, if your concern is privacy and security.
So, if we were to conclude something, it would be that hacking a blockchain is a rather thankless endeavor that requires enormous amount of computing power. And even if, theoretically speaking, it's something that can be considered possible, when it comes to practice, it's essentially impossible.
Start your learning journey and join the Blockchain Revolution!