Blog / Disruptive Technologies
Cybersecurity Social Engineering - The Human Shield (PART 1)
Categories

Why do we need to address social engineering in a cybersecurity context?
Because the stakes are high!
Did you know that ninety percent (90%) of cybersecurity breaches are caused by human error? Clearly, humans need to access computers to consume and manipulate information. Most of them use information in their everyday life, and for many, computers are at the core of their professional activities. Nowadays all economic sectors from government to industry, and from leisure to education, use computer systems. Without humans, there would not be a need for computers, and without computers, civilization would be very different!
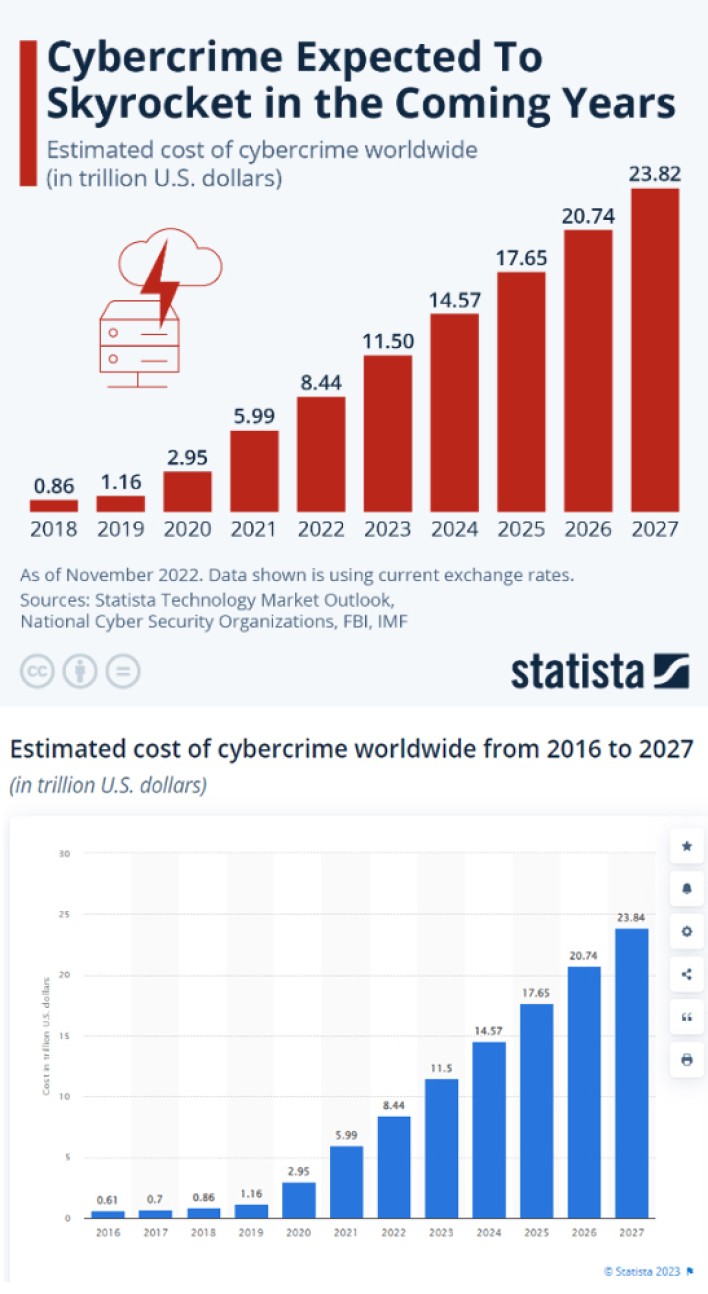
Therefore, humans are the weakest link in the cybersecurity chain because they hold the “keys” to the computers and they have the capacity to make arbitrary decisions. So cybersecurity it´s not just a technical problem, it is a people´s problem. A management problem. A psychological problem. One that we need to address urgently. Because threats are increasing and the potential costs are huge.
Social engineering technique: What it is
Computers are the weapons and computers are the targets, but the perpetrators are humans. We can build the most sophisticated security systems in the world, but if humans are manipulated to share their “keys”, hackers will have no problem getting through to the computer systems we are protecting. This type of cyber manipulation it´s called Social Engineering. It has many shapes and flavors; however, the methods used in social engineering have one thing in common. They always look to utilize the same channels their targets use to communicate (eMail, Phone, Social media, person-person…). There are two parts to social engineering. The “social” part is about the target person, whilst the “engineering” part is the information used to manipulate the target. This information is normally collected from various sources and crossed-referenced to complete a target schema profile. These profiles are then used to select the most effective methods to execute targeted hacking activities. Well-known types of social engineering attacks include pishing and baiting. Phishing is a type of cyber attack where the attacker sends fraudulent emails or messages to trick individuals into disclosing sensitive information or performing harmful actions. In Baiting, the attacker offers something enticing to a victim, such as a free download or gift, in order to trick them into downloading malware or providing sensitive information.
Cybersecurity Social Engineering: The Psychological Game
Cyber-security Social Engineering is about exploiting our psychology traits. Cyber criminals are playing our human emotions in their game of hacking. There´s nothing wrong with who we are, it is just that we are not yet used to differentiate our interaction with humans and computers. For instance, humans, we have something called the Sympathy Principle which is much needed in society, but easily useable by cybercriminals to ask favors and extract information. The Sympathy Principle is a social engineering tactic in which an attacker tries to exploit a victim's emotions, such as compassion or helpfulness, to gain their trust and obtain sensitive information. Another trick often used is the Art of Misdirection. As magicians do, cybercriminals will try to create an Illusion inside an Illusion to eliminate our critical thinking. Let's say that you’re told that you have been hacked, and to help, you need to do something such as share some information. These are two prominent practices used by criminal organizations to prepare cyber-attacks on a society that is not defenseless, but mostly unaware and unprepared to recognize cyber-treats.
Prevent Social Engineering: Embrace the Collective Mindset
In our second part of this two part series (coming soon!), we will explore how humans are generally driven to do things individually, and what drives the collective involvement. We will try to answer these key questions: What are the triggers that motivate people to protect the group rather than just focus on protecting themselves? And: What collaborative measures companies can look at to create a real collective human shield, instead of relying on individual actions?
Master Digital Transformation with Cybersecurity
Understanding cybersecurity is crucial when exploring the benefits and opportunities of digital transformation because as organizations increasingly rely on technology and digital processes, they become more vulnerable to cyber threats and cybersecurity social engineering. Failure to understand and address cybersecurity risks can lead to significant financial losses, reputational damage, and legal consequences. Thus, a comprehensive cybersecurity strategy is essential to ensure the safe and successful implementation of digital transformation initiatives. In ZIGURAT's Global MBA in Digital Transformation I will teach you cybersecurity skills and how to protect digital systems, networks, and sensitive information from unauthorized access, use, disclosure, disruption, modification, or destruction.





